Canvas Faces ShinyHunters Ransom Demand Amid Outage: What the Attack Means for Students, Schools, and Digital Education
For millions of students, Canvas is not just another website. It is the place where school happens.
Assignments live there. Grades live there. Lecture slides, quizzes, exam instructions, reading lists, class announcements, professor messages, group discussions, deadlines, and feedback all flow through the platform. For many universities, schools, and colleges, Canvas is the invisible digital hallway connecting teachers and students every day.
So when Canvas suddenly went down amid a reported cyberattack and ransom demand, the disruption felt immediate and personal.
Students trying to submit assignments or prepare for finals found themselves locked out. Some reportedly saw messages from a hacking group instead of their learning portal. Universities began issuing warnings. Schools scrambled for alternatives. Teachers moved communication to email, Zoom, Google Drive, or emergency backup systems. Parents and students wondered whether personal data had been exposed. And behind the outage, one name kept appearing in reports: ShinyHunters.
Some headlines have referred to “ShinyNet,” but the group most widely named in current reporting is ShinyHunters, a known cybercriminal group that has claimed responsibility for the incident. Reuters reported on May 8, 2026, that multiple U.S. college newspapers said Canvas had been hacked, with students at institutions including Harvard, the University of Pennsylvania, Duke, UCLA, and the University of Nebraska redirected to a message from ShinyHunters demanding contact by May 12. Instructure, the company behind Canvas, placed services into maintenance mode while investigating login issues and suspicious activity.
This is more than a temporary school-tech outage. It is a warning about the fragile dependency modern education has built around centralized digital platforms. When one widely used vendor is hit, thousands of institutions can feel the shock at once.
The Canvas outage is not only a cybersecurity story.
It is a story about finals week chaos, student data exposure, vendor risk, ransomware pressure, digital trust, and how deeply education now depends on systems most students never think about until they disappear.
What Happened to Canvas?
Canvas, the learning management system operated by Instructure, experienced a major cyber incident and outage affecting schools, colleges, and universities across multiple regions. Reports say users were blocked from accessing Canvas or redirected to a message attributed to ShinyHunters, a cybercriminal group claiming it had breached Instructure and obtained sensitive education-related data.
Reuters reported that students at several major universities encountered hacking messages when attempting to access Canvas, while Instructure placed services into maintenance mode and acknowledged login issues with Student ePortfolios.
AP reported that the cyberattack hit Canvas just as many students were preparing for final exams, disrupting access to lecture slides, grades, assignments, and academic resources. The report said some educators had to find alternate ways to support students and that some exams were postponed.
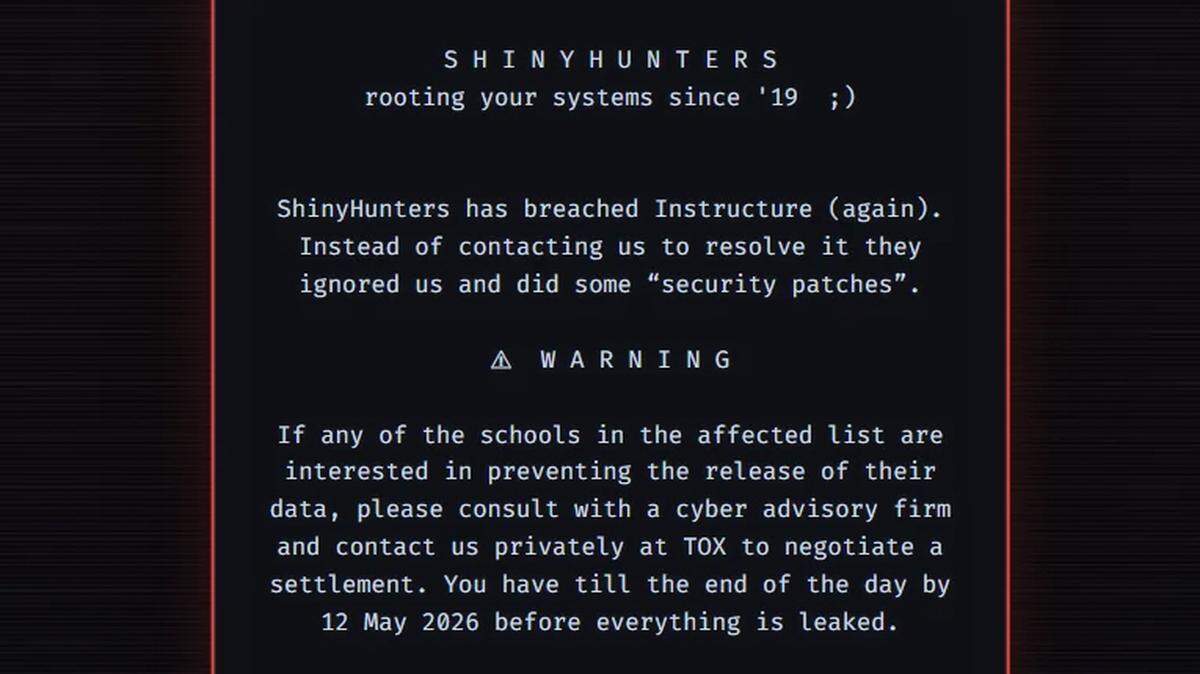
The Verge reported that students attempting to log in encountered a message from ShinyHunters threatening to leak data from thousands of schools unless a private settlement was arranged by May 12, 2026. The attackers claimed to have compromised data from around 9,000 schools and as many as hundreds of millions of students, teachers, and staff, though those numbers remain claims by the attackers and should be treated cautiously unless independently verified.
That distinction is important. In cyberattacks, threat actors often inflate numbers to increase pressure. Their claims may be partly true, exaggerated, or strategically framed. But even if the final verified impact is smaller than claimed, the incident is still serious because Canvas is deeply embedded in education worldwide.
Who Is ShinyHunters?
ShinyHunters is a cybercriminal group known for high-profile data theft and extortion activity. The group has been linked in reports to major breaches and ransom-style leak threats, often using stolen data as leverage.
AP described ShinyHunters as a hacking group believed to include young hackers from the U.S. and U.K., and said the Canvas incident resembled earlier education-sector breaches, including PowerSchool-related activity.
Inside Higher Ed reported before the outage that hackers had targeted Instructure with a “pay or leak” demand, warning the company to reach out before a leak and threatening “annoying” digital problems if ignored.
KrebsOnSecurity also linked the Canvas disruption to ShinyHunters and noted the group’s previous extortion behavior, including a reported earlier ransom demand involving the University of Pennsylvania.
For readers, the key point is simple: this does not appear to be a random glitch or ordinary maintenance issue. Current reporting describes it as a cyber incident involving a threat actor making extortion demands.
Why the Name “ShinyNet” Is Appearing
Some trending headlines and social posts have used the phrase ShinyNet when discussing the ransom demand. Based on current major reporting, the group at the center of the Canvas incident is ShinyHunters, not ShinyNet. Hindustan Times used a headline referring to “ShinyNet’s ransom demand,” but its related coverage also discusses the broader ShinyHunters-linked Canvas breach narrative.
This matters because cyber incidents often generate confusion quickly. Names spread across social media, headlines are rewritten, screenshots circulate, and users repeat what they see. In this case, the safer phrasing is: Canvas is facing a ransom threat from a group widely reported as ShinyHunters; some headlines have referred to ShinyNet.
That keeps the story accurate without ignoring what readers may be searching for.
What Data Was Reportedly Exposed?
Instructure and affected institutions have indicated that the involved data may include user-identifying and platform-related information. The University of Texas technology notice said Instructure disclosed on May 1, 2026, that the incident involved certain user data, including names, email addresses, student ID numbers, and messages among users. It also said Instructure found no evidence that passwords, dates of birth, government identifiers, or financial information were involved.
The Herald Sun reported similar details for affected Australian institutions, saying Instructure confirmed attackers accessed names, email addresses, student IDs, and inbox messages, but no passwords or financial details.
The Verge reported that ShinyHunters claimed access to sensitive information including student names, email addresses, ID numbers, and messages.
This kind of data may not sound as immediately dangerous as passwords or financial records, but it still matters. Names, school emails, student IDs, course details, and internal messages can be used for phishing, impersonation, harassment, social engineering, or targeted scams.
A stolen password is dangerous.
But a stolen educational identity map is also dangerous.
Why Messages Matter
One of the most concerning data categories mentioned in reports is messages among users.
Canvas messages can include routine academic communication, but they may also contain sensitive personal details. Students may message instructors about illness, disability accommodations, missed deadlines, family emergencies, grades, disciplinary concerns, financial hardship, mental health struggles, or academic disputes. Teachers may communicate with students about performance, extensions, conduct, or private course matters.
Even if no financial data or government identifiers were exposed, private educational messages can still be highly sensitive.
This is why schools should not treat the incident as a minor directory leak. If messages were accessed, the breach affects privacy, not just login inconvenience.
Why the Timing Was So Damaging
The Canvas outage hit during a brutal academic window: finals season.
AP reported that the cyberattack disrupted students preparing for final exams and prevented access to academic resources like lecture slides and grades. Some universities reportedly postponed exams or moved to alternate methods.
That timing amplified the impact. A Canvas outage in a quiet mid-semester week would still be disruptive. But during finals, it becomes academic chaos. Students may need access to study materials, assignment submissions, rubrics, professor announcements, online exams, feedback, and grade information. Faculty may need to manage deadlines, grade submissions, and exam logistics.
A learning management system is supposed to reduce friction. When it fails at the end of term, it becomes a single point of failure for the entire academic calendar.
That is one of the biggest lessons from the incident: education systems must have backup plans for critical academic periods.
The Outage Was a Trust Crisis
Every cyberattack has technical layers: credentials, tokens, cloud systems, access controls, monitoring, patches, incident response, logs, and forensic analysis.
But for students and teachers, the immediate issue is trust.
Can I submit my exam?
Can I access my grades?
Were my private messages exposed?
Can I trust the login page?
Should I click links from my university?
Is the maintenance message real?
Is my school telling me everything?
A platform like Canvas works because users trust it invisibly. They do not verify every page, every login flow, or every notification. They assume the system is safe because it belongs to the school. When a hacker message appears in the same place students normally see course content, that trust is shaken.
The real damage of a cyberattack is not only stolen data. It is the sudden feeling that the digital environment is no longer reliable.
Why Education Platforms Are Attractive Targets
Education platforms are valuable targets because they contain enormous amounts of personal information and serve large, interconnected populations.
A single platform may connect students, teachers, parents, staff, alumni, institutions, third-party tools, course archives, messages, grades, assignments, and integrations. Attackers do not need to breach every school separately if they can target a central vendor or cloud service.
The Next Web described the Canvas incident as a vendor-centered education breach, arguing that schools may be fully compliant internally yet still exposed when a dominant platform provider is compromised.
That is the vendor-risk problem in one sentence.
Universities and schools can train staff, enforce MFA, run audits, and maintain policies, but they still depend on external platforms. If a vendor is compromised, the blast radius can include thousands of institutions.
Modern education is not just digital.
It is vendor-dependent.
The Ransom Demand and the May 12 Deadline
Reports say ShinyHunters threatened to leak data unless a settlement or contact occurred by a deadline. The Verge reported that the hacker message demanded a private settlement by May 12, 2026.
WRAL reported that the group said affected schools could negotiate a settlement and had until May 12 to do so, while claiming Instructure ignored them and only applied security patches.
Ransom deadlines are a common extortion tactic. They create urgency, panic, and pressure. Attackers want victims to fear reputational damage, legal exposure, operational disruption, and public embarrassment. By putting a date on the threat, they turn stolen data into a countdown.
For institutions, the challenge is difficult. Paying does not guarantee deletion. Refusing can lead to leaks. Negotiating can create legal, ethical, and operational complications. Public communication must be careful while forensic work is ongoing.
This is why ransomware and data-extortion incidents are so damaging even when systems begin coming back online.
The outage may end quickly.
The breach response may last months.
What Schools Are Doing
Schools and universities have been issuing notices, warning students to avoid suspicious messages, and moving coursework or finals logistics to alternate channels.
Reuters reported that college newspapers at several major universities covered Canvas access disruptions and ShinyHunters messages.
The University of Texas said Instructure had disclosed a cybersecurity incident and listed the data types believed to be involved, while noting no evidence of passwords, birth dates, government IDs, or financial data.
ABC Australia reported that hundreds of thousands of students and teachers were unable to access schoolwork or submit assessments after Canvas access was paused, and that Instructure had said Canvas was available for most users while full restoration remained unclear.
The University of California system, according to reports summarized in incident trackers, instructed locations to block or redirect Canvas access out of caution after suspicious messages appeared on login pages.
The response varies by institution because Canvas is integrated differently across schools. Some may rely on it for nearly everything. Others may have backup communication systems and local copies of materials.
Why “Maintenance Mode” Confused Users
When a platform is placed into maintenance mode during a cyber incident, users often do not know whether the maintenance is normal, defensive, or part of the attack.
Instructure placed Canvas and related services into maintenance mode while investigating. Reuters reported that the company acknowledged login issues and placed services into maintenance mode as reports of hacking messages spread.
For students, that created confusion. A maintenance message during finals is already stressful. A maintenance message after seeing or hearing about a hacker ransom note is worse.
This is why crisis communication matters. Users need clear, repeated, official updates from institutions. They need to know whether they should log in, whether they should reset passwords, whether deadlines are extended, whether messages are safe, and where to find verified information.
During an incident, silence becomes a rumor factory.
What Students Should Do Now
Students should not panic, but they should be cautious.
First, follow official instructions from your school or university. Use trusted channels: official school websites, verified IT pages, official email accounts, and status pages.
Second, be careful with links. A breach involving email addresses and educational context creates phishing risk. Attackers may send fake Canvas updates, fake password-reset emails, fake grade alerts, fake exam links, or fake refund notices.
Third, do not reuse passwords. Even if Instructure says passwords were not involved, students often reuse passwords across platforms. A phishing wave after a breach can still compromise accounts.
Fourth, enable multi-factor authentication wherever available.
Fifth, save local copies of important academic materials when systems return, especially during finals. Do not assume continuous platform availability.
Sixth, ask instructors for alternate submission methods if Canvas remains unavailable.
Seventh, monitor official updates about whether your personal data was involved.
The most likely immediate risk for many students may not be direct account takeover through Canvas passwords. It may be follow-on phishing using exposed names, emails, course details, or school affiliation.
What Parents Should Watch For
Parents of K-12 students should be aware that school platforms often contain more information than they realize. Names, emails, student IDs, class data, teacher messages, and parent contact links can create social engineering opportunities.
Parents should watch for:
Fake school emails asking for payment.
Fake “student account” reset links.
Messages claiming urgent grade or discipline issues.
Requests for personal information.
Attachments pretending to be homework or school notices.
Unknown callers claiming to represent the school or Canvas.
If a message seems urgent, emotional, or financially demanding, verify through official school channels before responding.
Cybercriminals often exploit confusion after a breach. They know families are anxious and institutions are overwhelmed.
What Teachers and Faculty Should Do
Teachers and faculty should prepare alternate academic continuity plans.
That means keeping local copies of syllabi, readings, gradebooks where policy allows, exam instructions, assignment prompts, and class contact lists. It also means having a backup communication method for students, whether institutional email, a department site, or another approved channel.
Faculty should also be careful with private student information. If Canvas messages were accessed, instructors may need guidance from institutional privacy officers about what communications could be sensitive.
Teachers should avoid improvising insecure workarounds, such as collecting sensitive assignments through personal email, public links, or unapproved cloud folders without institutional guidance.
The right response is not chaos.
It is planned continuity.
What Institutions Should Learn
The Canvas incident should push schools to rethink digital resilience.
Every school using a major LMS should ask:
What happens if Canvas is unavailable during finals?
Do instructors have offline copies of critical materials?
Can students submit assignments through an emergency method?
Are gradebooks backed up securely?
Who communicates with students during a platform outage?
Are phishing warnings ready?
Do contracts require timely vendor breach notifications?
What data is stored in the LMS that does not need to be there?
Are messages retained longer than necessary?
Can schools temporarily disable vulnerable integrations?
Do students know where official status updates live?
The goal is not to abandon digital platforms. That is unrealistic. The goal is to avoid making one platform the only route through an academic emergency.
Education needs disaster recovery, not just software subscriptions.
The Vendor-Risk Problem
The Canvas incident shows how vendor concentration can create systemic risk.
When thousands of institutions depend on a single platform, a vendor breach becomes a sector-wide event. Each school may have its own IT team, but the dependency is shared. This is similar to what happens in healthcare, finance, cloud computing, or supply-chain software.
The Next Web argued that the breach illustrates how compliance at the school level may not prevent damage from a vendor-level compromise.
That is a hard lesson for education. Schools may believe they have outsourced technical complexity. But they have not outsourced responsibility to students, families, regulators, or the public. When a vendor fails, institutions still face the consequences.
Vendor due diligence must become more serious. That includes security reviews, breach notification requirements, data minimization, access controls, independent audits, incident simulations, and contractual accountability.
Was Financial Data Exposed?
Current institutional notices and reports indicate that Instructure found no evidence that passwords, dates of birth, government identifiers, or financial information were involved. The University of Texas notice specifically stated that Instructure had found no evidence those categories were involved.
The Herald Sun similarly reported that no passwords or financial details were confirmed as compromised in the information shared by Instructure.
That is reassuring, but not a reason to ignore the incident. Personal identifiers and messages can still be abused. Attackers do not need bank data to create harm. They can use education data to craft believable scams.
A student may ignore a generic phishing email.
They may not ignore one that includes their school, course, teacher, student ID, or real message context.
Could Grades Have Been Exposed?
Current reports emphasize names, emails, student IDs, and messages. Some attacker claims and local reports have mentioned broader records, but the exact confirmed scope remains under investigation. AP reported that ShinyHunters claimed it accessed billions of private messages and records, but such claims had not been independently verified in full.
Until institutions provide final breach notifications, students should avoid assuming either worst-case or best-case scenarios. The confirmed public details may evolve as forensic analysis continues.
Schools should be transparent when they know more. Students deserve specific answers: Were grades accessed? Were assignments accessed? Were files accessed? Were messages accessed? Which dates? Which users? Which courses?
Cybersecurity trust depends on precision.
Why Attackers Target Finals Week
If the timing was intentional, finals week is a pressure multiplier.
Attackers know institutions are more likely to feel desperate when disruption affects exams, grades, deadlines, and graduation processes. Operational pressure can influence ransom decisions. A school may tolerate some downtime in summer. It may panic during final exams.
AP reported that the attack disrupted students during final-exam periods at some colleges and universities.
This is a known ransomware dynamic. Attackers often strike when victims are least able to absorb disruption: hospitals during care operations, retailers during holidays, schools during exams, governments during critical deadlines.
The cruelty is strategic.
Why Students Saw Hacker Messages
One alarming feature of the incident was that students reportedly saw messages from ShinyHunters when attempting to access Canvas. Reuters reported that students at multiple universities were blocked from Canvas and redirected to a hacking-group message.
This kind of visible defacement or redirect is psychologically powerful. It does not merely steal data quietly. It announces control. It turns every user into a witness. It increases pressure on the vendor and institutions because the breach becomes impossible to keep contained.
From an attacker’s perspective, that visibility is part of the extortion strategy.
From a user’s perspective, it is alarming because the normal trust boundary collapses. The school platform appears to have been replaced by a criminal message.
That is why the incident felt so dramatic.
The Role of Status Pages
During SaaS outages, status pages are supposed to provide official truth. Instructure’s status page became an important reference point as services were placed into maintenance mode and restored.
However, status pages can be insufficient if they do not clearly explain the security nature of the incident. Users want to know not only whether Canvas is up, but whether it is safe to use, whether data was exposed, and whether there are actions they should take.
A good incident status page should answer:
What systems are affected?
Is this a security incident?
What user data may be involved?
Is login safe?
Should users reset passwords?
Are messages or files affected?
When is the next update?
Which institutions are impacted?
Where should students report suspicious emails?
Technical uptime updates are not enough during a data breach.
People need security guidance.
Why This Could Lead to Phishing Waves
After a breach, the second attack often begins.
If attackers or other criminals have access to lists of student emails and school affiliations, they can send highly convincing phishing messages. These may pretend to be from Canvas, Instructure, the university IT department, financial aid, professors, registrar offices, exam portals, or student services.
Messages may claim:
“Reset your Canvas password now.”
“Your assignment was not submitted.”
“Your final exam has been rescheduled.”
“Verify your student ID.”
“Download your grade report.”
“Your financial aid is paused.”
“Your data was leaked; click here to check.”
“Pay to protect your account.”
Students should be especially careful during the weeks after the outage. The panic around finals and data exposure makes people more likely to click.
The breach may be one event.
The scams that follow may be many.
What Instructure Has Said Publicly
Institutional notices referencing Instructure say the company disclosed a cybersecurity incident involving certain user data and took steps to secure platforms. GovTech reported that Instructure said on May 2 it had revoked privileged credentials and access tokens, deployed security patches across affected systems, and intensified monitoring across platforms.
Reuters reported that Instructure placed services into maintenance mode while investigating, but had not provided additional comments beyond initial status updates at the time of that report.
As with many active cyber incidents, public details may remain limited while forensic investigations continue. That can be frustrating for users, but premature statements can also be inaccurate.
Still, schools and users need timely, plain-language guidance. The balance between investigation and communication is difficult, but silence is not neutral. It can increase fear and speculation.
Is Canvas Back Online?
Availability appears to be changing by region and institution. ABC Australia reported that Instructure said Canvas was available for most users, but it remained unclear when systems would be completely back online.
Some institutions may restore access earlier than others depending on local decisions, redirects, blocks, identity-provider settings, and guidance from Instructure.
Users should not rely on social media rumors to determine whether Canvas is safe or available. They should check official school IT updates and Instructure’s status information.
A platform can be technically online while some schools still choose to block access temporarily out of caution.
The Bigger Lesson: Education Needs Cyber Resilience
The Canvas incident should become a wake-up call for the education sector.
Schools have spent years moving learning into centralized platforms. That has real benefits: easier communication, online submissions, remote learning, grade tracking, accessibility tools, and integrations. But it also creates concentration risk.
A single outage can disrupt thousands of classrooms.
A single breach can expose millions of users.
A single ransom note can interrupt finals.
Digital education needs resilience built into its design. That means offline access to critical materials, backup submission channels, emergency communication procedures, local academic continuity plans, stronger vendor oversight, and regular cyber drills.
Schools run fire drills.
They need LMS outage drills too.
The Human Cost of “Just an Outage”
To outsiders, a platform outage may sound minor. Students can wait, right?
Not always.
A Canvas outage during finals can affect graduation timelines, scholarship requirements, visa-status obligations, accommodation deadlines, athletic eligibility, job applications, and mental health. Students may already be under pressure. Losing access to assignments or exams can feel devastating.
Teachers also face stress. They may need to redesign assessments overnight, extend deadlines, answer hundreds of emails, and reassure students without having enough information themselves.
The phrase “Canvas is down” hides a lot of human anxiety.
That is why cyberattacks on education are especially cruel. They target systems used by young people, educators, and public institutions already operating under pressure.
What Happens Next?
The next phase will likely involve several parallel tracks.
Instructure will continue forensic investigation and service restoration.
Schools will issue local guidance and breach notifications if required.
Threat actors may publish more claims, samples, or threats near ransom deadlines.
Students and staff may receive phishing attempts.
Regulators or government cybersecurity agencies may review the incident.
Institutions may reassess vendor contracts and LMS continuity planning.
Some exposed users may eventually receive formal notices explaining what information was involved.
The key date in the ransom threat reported by multiple outlets is May 12, 2026, though ransom deadlines can change or be used strategically by attackers.
The story is still developing. Early reporting is useful but incomplete. Claims by attackers should not be treated as final proof. Official notifications may take time.
Final Verdict: Canvas Outage Shows the Weak Point in Digital Education
The Canvas cyberattack and ShinyHunters ransom demand are more than a dramatic tech headline. They expose one of the biggest vulnerabilities in modern education: the dependence of thousands of institutions on a small number of centralized platforms.
Current reports say Canvas users at major schools were blocked or redirected to hacker messages, Instructure placed services into maintenance mode, and ShinyHunters threatened to leak data unless a settlement was arranged by a May 12 deadline.
The data reportedly involved may include names, email addresses, student ID numbers, and messages, while Instructure has said it found no evidence that passwords, birth dates, government identifiers, or financial information were involved.
That is reassuring, but only partly. Educational messages and identifiers can still be sensitive. The outage itself disrupted learning during finals. The ransom threat created fear. The visible hacker message damaged trust. And the scale of Canvas’s adoption turned a vendor incident into a global education problem.
The lesson is clear: schools cannot treat learning platforms as invisible infrastructure anymore. They are critical systems. They need backup plans, stronger vendor oversight, data minimization, transparent communication, and cyber resilience.
Canvas may come back online.
But the trust questions will last much longer.
FAQ: Canvas, ShinyHunters, and the Ransom Demand
What happened to Canvas?
Canvas experienced a major cyber incident and outage affecting schools and universities. Reports say students attempting to access Canvas were redirected to a message from ShinyHunters, a hacking group claiming responsibility for a breach.
Who is behind the Canvas outage?
Current major reports name ShinyHunters as the group claiming responsibility. Some headlines have used the name “ShinyNet,” but the widely reported threat actor is ShinyHunters.
What did ShinyHunters demand?
Reports say ShinyHunters threatened to leak stolen data unless Instructure or affected parties arranged a private settlement by a deadline reported as May 12, 2026.
What data was exposed in the Canvas breach?
Institutional notices say Instructure disclosed that involved data may include names, email addresses, student ID numbers, and messages among users. Instructure said it found no evidence that passwords, dates of birth, government identifiers, or financial information were involved.
Were Canvas passwords stolen?
Based on current institutional notices, Instructure has said it found no evidence that passwords were involved. Users should still remain alert for phishing and follow any password-reset guidance from their school.
Why did the Canvas outage matter so much?
The outage happened during finals season for many institutions, disrupting access to assignments, lecture materials, grades, and exams. AP reported that some schools had to postpone exams or find alternate methods.
How many schools were affected?
ShinyHunters claimed thousands of schools were affected, with reports citing around 9,000 institutions, but the full verified scope remains under investigation. Attacker claims should be treated cautiously until confirmed.
Is Canvas back online?
Availability appears to vary. ABC Australia reported that Instructure said Canvas was available for most users, though full restoration remained unclear. Students should check official school IT updates.
What should students do after the Canvas breach?
Students should follow official school guidance, avoid suspicious emails or links, enable multi-factor authentication where available, avoid password reuse, and watch for phishing attempts pretending to be Canvas or school IT.
What is the bigger lesson from this incident?
The incident shows that learning management systems are critical infrastructure for education. Schools need backup plans, stronger vendor-risk management, data minimization, and emergency communication procedures for major LMS outages or breaches.